As platforms grow to serve large enterprises, one recurring risk pattern becomes clear: security controls drift and fail silently when implemented inconsistently across endpoints. New endpoints get added, existing ones evolve, and over time, authorization rules either lag behind or diverge subtly across teams and product lines.
At Eightfold, our platform serves some of the world’s largest enterprises across talent acquisition, workforce planning, and career development. Access control is not incidental to what we do. An authorization failure in our system is a compliance issue and a direct breach of customer trust.
To address this class of issues systematically, we built a centralized Endpoint Protection Framework that enforces validation at the request boundary, so every incoming request is evaluated consistently before it reaches business logic.
This post explains why we built it, how it works, and how we rolled it out safely at scale.

Why a request-boundary protection layer
1. Security failures tend to be structural, not local
Most privilege escalation and authorization issues are not caused by complex logic bugs. They are caused by missing or inconsistent enforcement. When every endpoint is responsible for remembering the right checks, drift is inevitable. A new endpoint gets added with a minimal check. An existing one evolves without updating its permissions. A penetration test (pentest) surfaces the gap months later.
Enforcing controls at the request boundary eliminates entire classes of mistakes before they ship.
2. Authorization belongs at the boundary, not just deep in handlers
Endpoints often start life with minimal checks and accrete logic over time. That is fragile. Central enforcement ensures:
- access rules are evaluated before handlers execute
- authorization logic is uniform across the codebase
- mistakes are caught early and visibly
This also provides a clean defense-in-depth layer while permanent fixes are developed.
3. Client-side controls are not security controls
Repeated pentest findings reinforce a well-known rule: anything enforced only in the UI will be bypassed.
Locked fields, disabled inputs, or hidden controls offer no protection unless the server explicitly validates requests. A centralized server-side validation layer provides one consistent place to enforce those rules.
4. Object-level access requires explicit enforcement
Even when a user is correctly authorized to access an endpoint, they may not be authorized to access the specific resource referenced in the request. Insecure Direct Object Reference (IDOR) vulnerabilities arise when requests carrying resource identifiers are not validated against the requesting user’s actual access rights. This class of issue is consistently among the most common findings in enterprise security audits, and it requires object-level access checks, not just endpoint-level ones.
Architecture: enforced for every request
The framework integrates into the top-level request lifecycle, ensuring validation runs before any endpoint-specific code executes.
At a high level:
- Incoming requests are intercepted at the request boundary
- A validation pipeline runs in sequence; the first phase that fails short-circuits the rest
- The framework enforces:
- input validation (pattern blocking, injection prevention)
- endpoint registry checks (is this endpoint known?)
- user-mode allowlists (who can access, and via which HTTP methods)
- resource-level access checks (does this user have access to this specific object?)
- On failure:
- enforcement mode blocks the request
- monitor-only mode logs violations without blocking
This makes enforcement central, deterministic, and auditable.
Three layers of access control
1. Endpoint registry: the perimeter
Every endpoint must be explicitly registered before it can serve traffic. An unregistered endpoint is flagged at development time as a hard error and logged in production.
This default-deny posture changes the development workflow in a meaningful way: adding an endpoint requires a deliberate act of registration, which forces a decision about access policy before the code ships. The registry is the authoritative record of every API surface in the system.
2. User-mode allowlisting: who can access and how
Endpoints explicitly declare which user roles are allowed access and which HTTP methods each role may use.
Key behaviors:
- Default deny: if a role is not explicitly listed, access is denied
- Public access must be declared explicitly and used sparingly
- Expanding access to new roles is a deliberate, reviewable decision
This enforces least-privilege by default and makes access intent visible in configuration rather than buried in handler code.
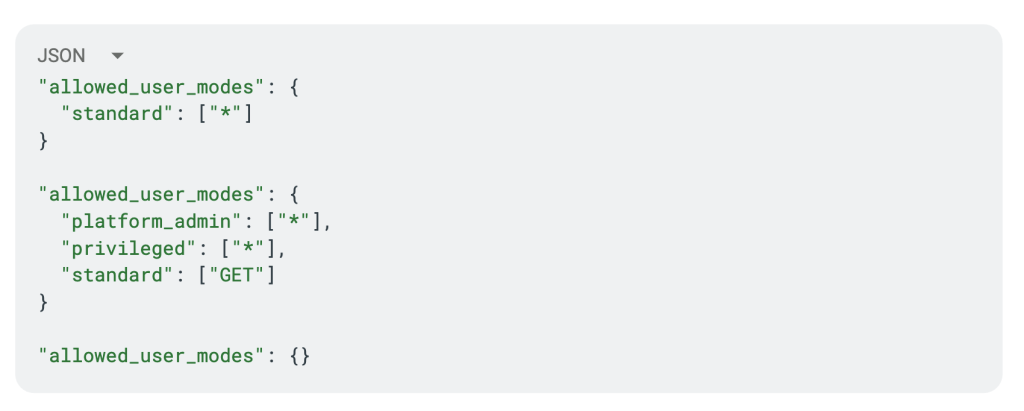
A user satisfies the check if any configured mode matches their session. This union semantic has a direct implication: adding a mode widens access, it does not restrict it. Endpoint owners should list only the roles that genuinely require access.
3. Resource-level access: closing the IDOR gap
The third layer checks that the specific object referenced in the request is accessible to the requesting user. For each resource identifier in the request, the framework loads the object and evaluates whether the user holds view or edit access rights.
This layer is configured per endpoint by declaring which request parameters carry resource identifiers and what access level is required. The framework handles extraction automatically across different input shapes, whether identifiers are passed as single values, comma-separated strings, or JSON arrays. A single unauthorized identifier in a batch request denies the entire request.
When in doubt, requiring edit-level access is the safer default. It is always easier to relax a restriction with evidence than to discover an over-permissive rule in production.
Centralized input validation
Authorization is only half the story. The framework also provides a pluggable architecture for standardizing what inputs are allowed across all endpoints.
Through a validation scheme registry, teams can enforce field-level rules including:
- Pattern blocking (XSS, injection)
- Structural and length constraints
- Custom validation logic per endpoint
Benefits:
- Eliminates ad-hoc validation scattered across handlers
- Ensures server-side enforcement even when the UI restricts inputs
- Creates a single place to expand coverage as new threat patterns emerge
This directly addresses common bypass techniques seen in real-world security testing.
Scale: distributing ownership without losing control
With a platform spanning multiple product lines and tens of engineering teams, a single shared configuration file for endpoint permissions would be a coordination bottleneck.
Instead, permission configuration is partitioned by product area, with each team owning their section. Access configuration changes require an automated security team review before merging, enforced at the repository level via code ownership rules. This is not advisory. It is a hard requirement that cannot be bypassed.
To make initial adoption tractable across hundreds of existing endpoints, we built a generation tool that introspects the running application and produces skeleton configuration entries for every registered endpoint. Teams received pre-populated files and were responsible for filling in the access policy for their own APIs, distributing the judgment work to the people who know each API best.

Safe rollout: monitor first, enforce deliberately
Because this framework sits in front of every endpoint, rollout safety is critical. A misconfigured rule that incorrectly blocks a legitimate request is a production incident.
1. Monitor-only (dark launch) mode
Every validation phase can operate in warn-only mode, logging violations without blocking requests. Before any enforcement was activated, all validation ran in a dark launch (running in observation-only mode without blocking traffic) across production traffic. This gave us a ground-truth view of what enforcement would look like, surfaced misconfigured entries early, and gave teams time to correct their configurations before users were affected.
Dark launch is not a brief staging step. It is a deliberate observation period, held until the data is unambiguous.
2. Independent feature flag rollout
Each validation phase is gated independently. The registry check, the permission check, and the object-level check can each be enabled or rolled back without affecting the others. This allowed us to validate each layer’s correctness in isolation and meant that a problem in one phase did not force a rollback of the entire framework.
3. Runtime overrides for rollout control and incident response
Configuration can be updated at runtime without a code deploy. This served two operational needs: graduating endpoints from dark launch to enforcement as confidence built, and emergency access revocation during incidents without waiting for a deployment cycle. For a framework that touches every request, the ability to change enforcement behavior in seconds rather than minutes is operationally critical.
Observability
The framework emits structured logs and counters at every decision point. Every denied request, in both enforcement and dark launch modes, records the endpoint, the user context, and the specific check that failed.
This investment paid off in three ways:
- Coverage visibility: at any point, we can see exactly which endpoints are under full enforcement, which are in dark launch, and which have not yet been configured. Partial coverage is not a security posture, and the gap must be visible.
- Early misconfiguration detection: unexpected spikes in violations during dark launch surfaced configuration errors within minutes, before they affected users.
- Signals for moving to enforcement: the dark launch violation rate for an endpoint is the primary signal for whether it is ready to move to full enforcement. Data replaces guesswork.
Operational impact
One effective early enforcement milestone is blocking unauthenticated access to internal and administrative endpoints by default. During rollout, structured monitoring queries surface:
- Unauthorized access attempts hitting protected endpoints
- High-volume violation patterns that signal misconfiguration rather than attacks
- Endpoints that require rule refinement before enforcement can be graduated
This helps teams converge quickly and systematically.
Summary
The Endpoint Protection Framework moves from best-effort, per-endpoint enforcement to a default-secure, centrally governed model. By enforcing layered validation at the request boundary, we:
- Prevent privilege escalation before it ships
- Eliminate authorization drift across endpoints and teams
- Close IDOR vulnerabilities at the framework level, not the handler level
- Enforce least-privilege by default
- Roll out safely to a live system without the risk of a disruptive all-at-once cutover
Most importantly, this approach makes secure behavior the default, not something developers have to remember to add on every endpoint they write.
Security at scale is not a single project with a completion date. It is an ongoing posture. The measure of success is a platform where “is this endpoint correctly protected?” has a verifiable answer, and where that answer stays correct as the system continues to grow.